Mastering Secure Deployment and Configurations: An In-Depth Guide to Best Practices and Strategies
In today’s digital landscape, ensuring the security of applications and systems during deployment is paramount. Misconfigurations and insecure deployment practices are among the leading causes of security breaches. This comprehensive guide delves into the critical aspects of secure deployment and configurations, providing detailed insights, best practices, and strategies to safeguard your infrastructure. Whether you’re a…
Read morePOSTED BY
Secure Debug
Mastering Secure SDLC: An In-Depth Guide to Integrating Security into the Secure Software Development Life Cycle
In the ever-evolving landscape of cybersecurity, integrating security into the Secure Software Development Life Cycle (SDLC) is no longer optional—it’s imperative. As cyber threats become more sophisticated, ensuring that security measures are embedded at every phase of software development is crucial. This comprehensive guide delves deep into Secure SDLC practices, providing insights, methodologies, tools, and…
Read morePOSTED BY
Secure Debug
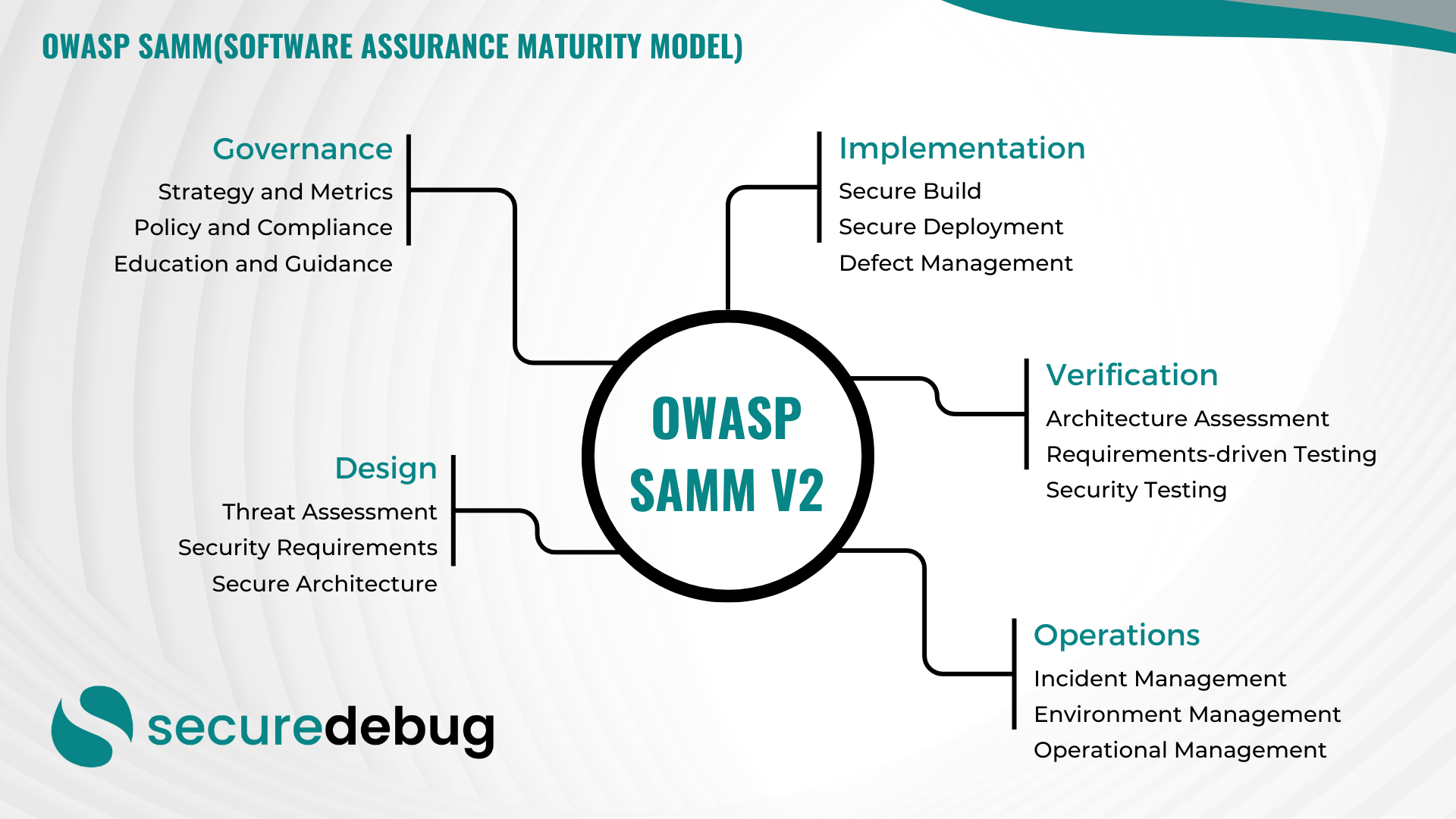
Comprehensive Guide to Implementing OWASP SAMM v2
Comprehensive Overview of OWASP Software Assurance Maturity Model (SAMM) Version 2 Introduction to OWASP SAMM v2 The OWASP Software Assurance Maturity Model (SAMM) Version 2 is an evolutionary framework designed to assist organizations in developing, enhancing, and maintaining a robust software security posture. As part of the Open Web Application Security Project (OWASP), SAMM provides…
Read morePOSTED BY
Secure Debug
The Role of Threat Modeling in DevSecOps
The Role of Threat Modeling in DevSecOps As cybersecurity threats continue to evolve, organizations must adopt robust security practices to protect their digital assets. DevSecOps, a methodology that combines development, security, and operations, has gained significant traction in recent years. One critical aspect of DevSecOps that plays a vital role in ensuring secure software development…
Read morePOSTED BY
Okan YILDIZ
Securing Cloud-Native Applications: A Comprehensive Guide
Securing Cloud-Native Applications: A Comprehensive Guide Welcome to Secure Debug’s blog! In this post, we will delve into the crucial topic of cloud-native security and explore various aspects to help you protect your applications and data in cloud-native environments. Understanding Cloud-Native Security Cloud-native applications are built using microservices architecture, containerization, and orchestration platforms like Kubernetes.…
Read morePOSTED BY
Okan YILDIZ
Enhancing Cybersecurity with Burp Suite, DevSecOps, SAST, and DAST
Enhancing Cybersecurity with Burp Suite, DevSecOps, SAST, and DAST Welcome to the Secure Debug blog! In this post, we will explore the powerful tools and practices that can significantly enhance your cybersecurity efforts. We’ll delve into the world of Burp Suite, DevSecOps, SAST (Static Application Security Testing), and DAST (Dynamic Application Security Testing) to understand…
Read morePOSTED BY
Okan YILDIZ
Implementing DevSecOps for Enhanced Cybersecurity
Introduction DevSecOps, a combination of Development, Security, and Operations, is an approach that emphasizes integrating security practices throughout the software development lifecycle. By adopting DevSecOps, organizations can proactively address cybersecurity threats and vulnerabilities from the early stages of development. Benefits of DevSecOps 1. Early Vulnerability Detection: DevSecOps allows for continuous monitoring and testing of code,…
Read morePOSTED BY