Mastering Secure Deployment and Configurations: An In-Depth Guide to Best Practices and Strategies
In today’s digital landscape, ensuring the security of applications and systems during deployment is paramount. Misconfigurations and insecure deployment practices are among the leading causes of security breaches. This comprehensive guide delves into the critical aspects of secure deployment and configurations, providing detailed insights, best practices, and strategies to safeguard your infrastructure. Whether you’re a…
Read morePOSTED BY
Secure Debug
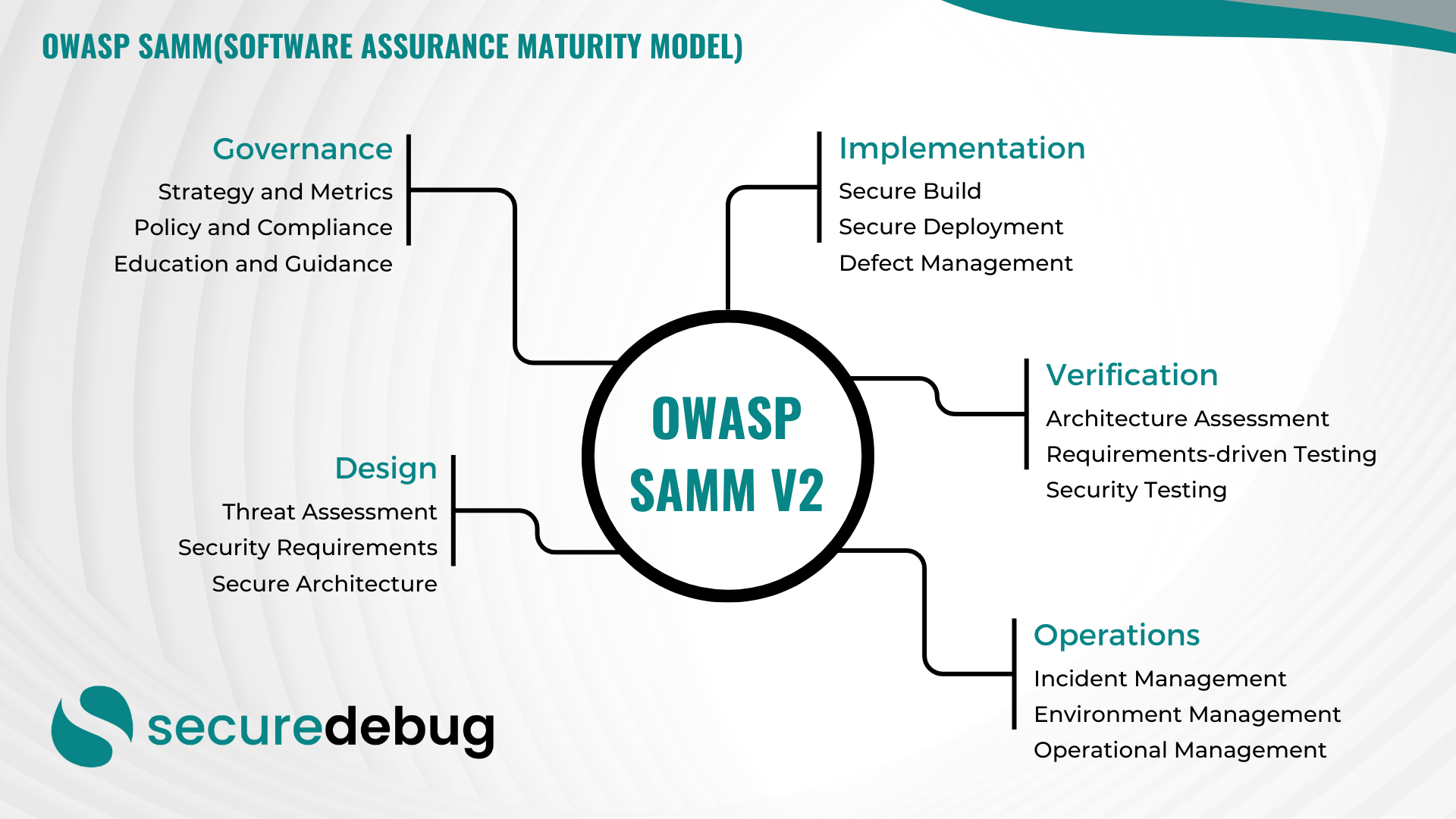
Comprehensive Guide to Implementing OWASP SAMM v2
Comprehensive Overview of OWASP Software Assurance Maturity Model (SAMM) Version 2 Introduction to OWASP SAMM v2 The OWASP Software Assurance Maturity Model (SAMM) Version 2 is an evolutionary framework designed to assist organizations in developing, enhancing, and maintaining a robust software security posture. As part of the Open Web Application Security Project (OWASP), SAMM provides…
Read morePOSTED BY
Secure Debug
Secure IoT Deployment: Ensuring the Safety of Connected Devices
Secure IoT Deployment: Ensuring the Safety of Connected Devices Internet of Things (IoT) devices have become an integral part of our lives, revolutionizing how we interact with technology. From smart homes to industrial automation, IoT devices offer convenience and efficiency. However, with this increased connectivity comes the need for robust cybersecurity measures to protect sensitive…
Read morePOSTED BY