Comprehensive Guide to Implementing OWASP SAMM v2
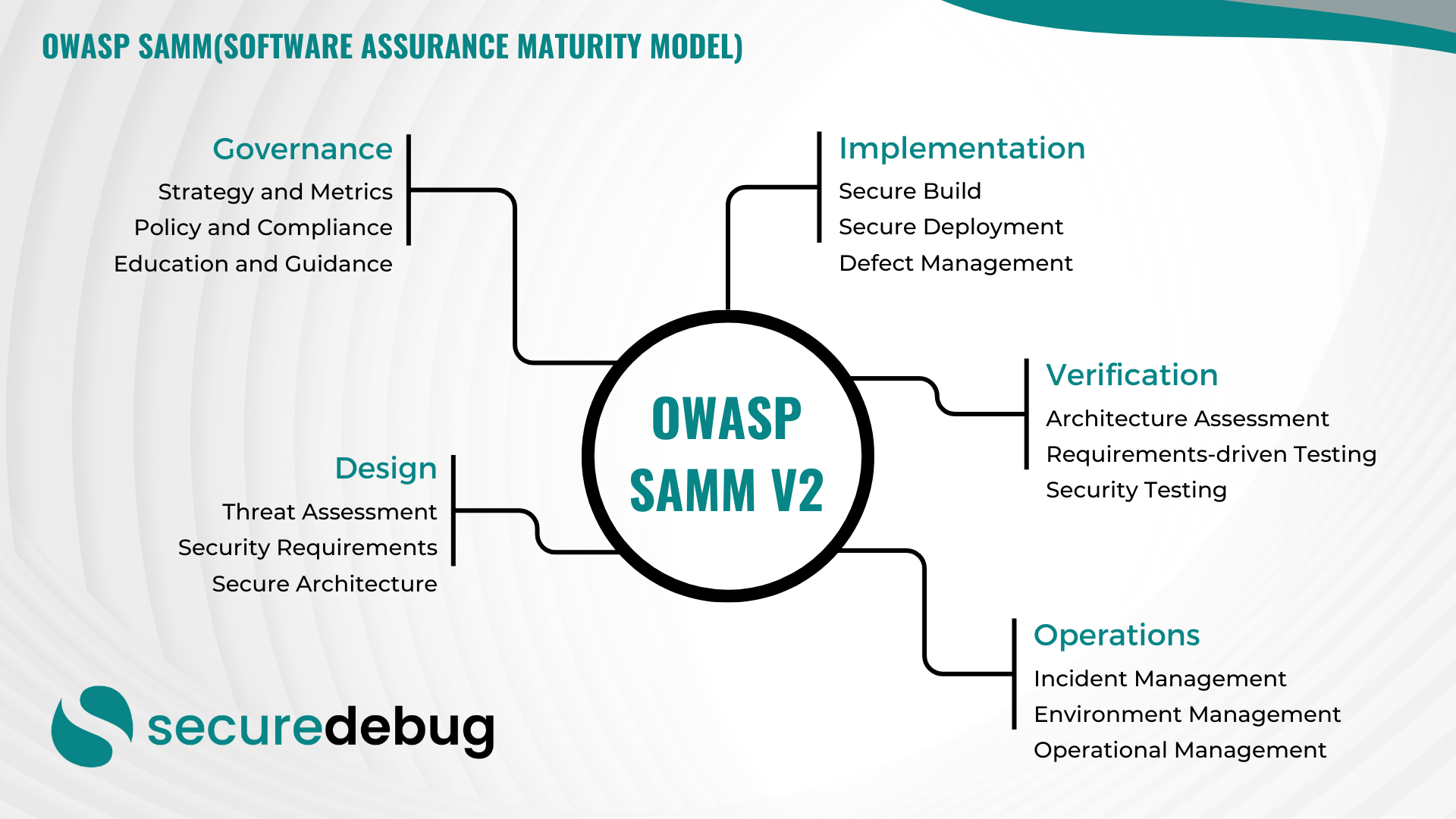
Comprehensive Overview of OWASP Software Assurance Maturity Model (SAMM) Version 2 Introduction to OWASP SAMM v2 The OWASP Software Assurance Maturity Model (SAMM) Version 2 is an evolutionary framework designed to assist organizations in developing, enhancing, and maintaining a robust software security posture. As part of the Open Web Application Security Project (OWASP), SAMM provides…
Read morePOSTED BY
Secure Debug
The Role of Threat Intelligence in Enhancing Network Security
The Role of Threat Intelligence in Enhancing Network Security Network security is a critical aspect of protecting sensitive data and ensuring the smooth operation of organizations. With the ever-evolving threat landscape, it is essential to implement proactive measures to detect and prevent cyber threats. One such measure is the utilization of threat intelligence. Threat intelligence…
Read morePOSTED BY
Okan YILDIZ
The Future of Cybersecurity: Artificial Intelligence and Machine Learning
The Future of Cybersecurity: Artificial Intelligence and Machine Learning As technology evolves, so do the methods employed by cybercriminals to exploit and compromise digital systems. Therefore, cybersecurity measures must also advance to keep pace. One of the most promising ways to achieve this is through the integration of Artificial Intelligence (AI) and Machine Learning (ML)…
Read morePOSTED BY